- NordVPN researchers have uncovered a major phishing scam
- Scammers pretend to be global employers like Meta, Disney, Spotify
- Cybercriminals use fake job sites to steal job seekers’ Facebook logins
The job market is tough enough without having to avoid cyber criminals. But according to new research from NordVPN, hackers are now posing as recruiters for the world’s biggest companies to hijack the social media accounts of unsuspecting job seekers.
The cybersecurity firm’s Threat Intelligence unit uncovered a phishing campaign targeting the names of major employers, including Meta, Disney, Coca-Cola, and Spotify.
Rather than directly stealing your money, the service is designed to silently harvest your Facebook information. With social media accounts often linked to other sensitive applications and services, a compromised Facebook login can quickly turn into a devastating privacy breach.
If you want to protect your personal data while applying for roles online, using one of the best VPN services with a built-in security system and malicious tracker blocking is a smart first step. However, staying completely safe from phishing requires a deep understanding of how these multi-stage scams really work.
From fake job offers to full account hijacking
The campaign begins with a professional-looking cold email, often sent through official platforms such as Google AppSheet to bypass standard spam filters.
These messages include clean language and target victims whose contact information may have been leaked from platforms such as LinkedIn or exposed in previous data breaches.
Clicking on the email link takes victims to a “HUB” site (such as careers.meta-findyourjob[.]com).
Interestingly, NordVPN discovered that these sites include a clever built-in avoidance strategy. When a security scanner or analyzer visits the URL directly, they only see a blank, harmless web page. The malicious “Search job” button only works if the site is launched by a unique link embedded in a phishing email.
When the victim clicks, they land in a middleware that unmistakably mimics the job board of a legitimate business. Researchers have identified several fake sites, including connect.spotifycareerapply[.]com for Spotify and jobquest.wdcfuturesteps[.]com for Disney.
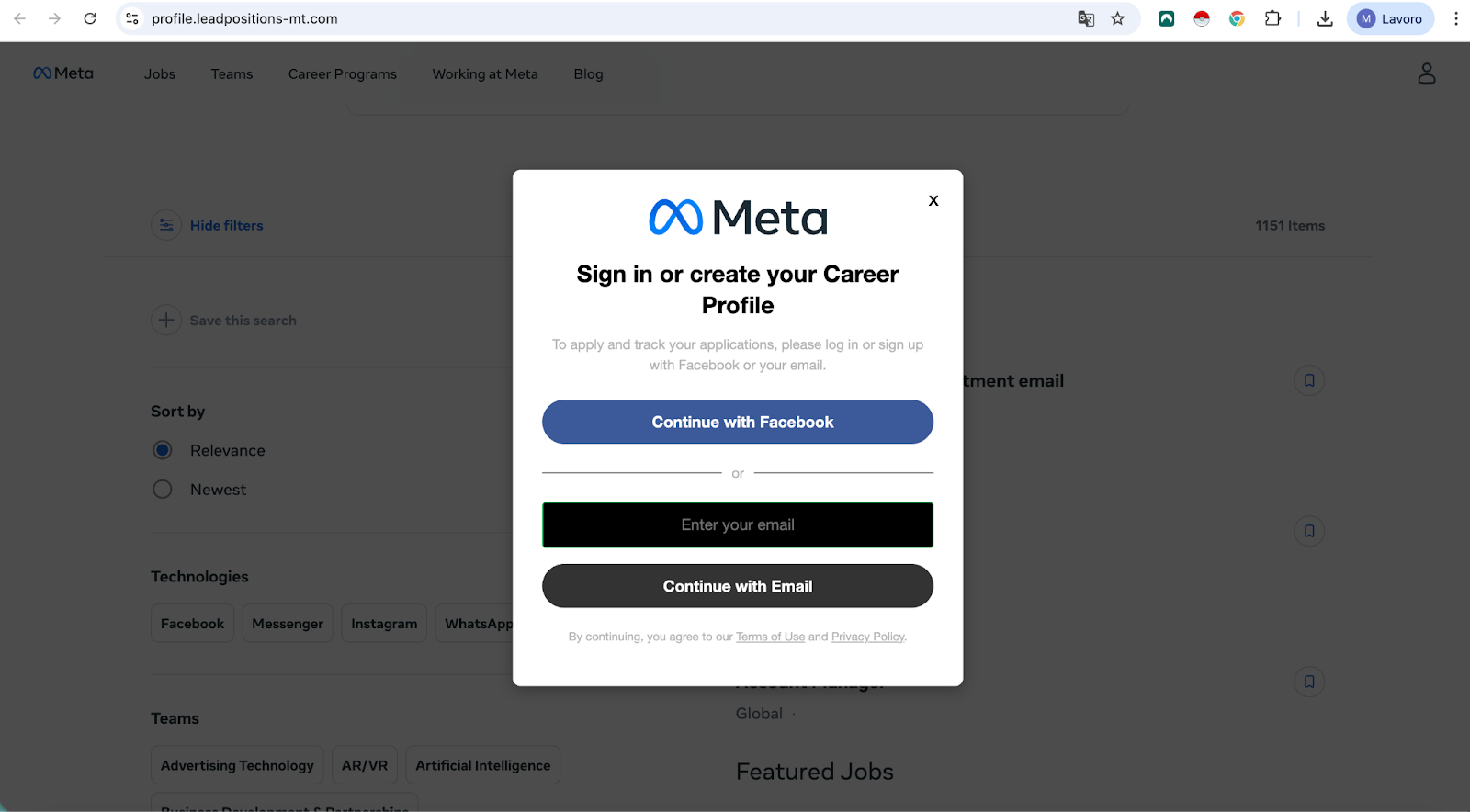
The trap finally closes when the applicant clicks “Apply.” Instead of a standard application form, they were met with a request to log in via Facebook to proceed. This fake login page captures the victim’s username and password, giving attackers complete control over the account.
Domininkas Virbickas, product director at NordVPN, explains that job seekers are “uniquely vulnerable” to these types of attacks as they are already in the mindset of sharing personal information and following instructions from contacts they don’t know.
“Such campaigns exploit that trust using sophisticated communications and convincing fake job sites that are almost indistinguishable from the real thing,” Virbickas said.
How to stay safe while job hunting
To protect yourself, NordVPN recommends making a habit of validating the URL before entering any personal data. Legitimate mega-brands will always host their job pages on legitimate, visible domains, not random third-party links.
The same rule applies to public access orders. The actual “Sign in with Facebook” button will always safely redirect you to the main page facebook.com background. If the URL bar shows anything else, close the tab immediately.
If you’re still in doubt, I recommend running the link with NordVPN’s URL checker tool or similar software. It is completely free to use for anyone, even those who do not have an active NordVPN subscription.
Finally, NordVPN suggests always enabling two-factor authentication (2FA) on all your social media profiles. Even if a phishing page manages to steal your password, 2FA acts as an important safety net that prevents attackers from accessing your account.
Follow TechRadar for Google news again add us as a favorite resource to get our expert news, reviews, and opinions in your feed. Be sure to click the Follow button!



